Speaking at the RSA security conference last week, Microsoft engineers said that 99.9% of the compromised accounts they track every month don’t use multi-factor authentication, a solution that stops most automated account attacks.
The cloud giant said it tracks more than 30 billion login events per day and more than one billion monthly active users.
Microsoft said that, on average, around 0.5% of all accounts get compromised each month, a number that in January 2020 was about 1.2 million.
While all account hacks are bad, they are worse when the account is for enterprise use. Of these highly-sensitive accounts, only 11% had a multi-factor authentication (MFA) solution enabled, as of January 2020, Microsoft said.
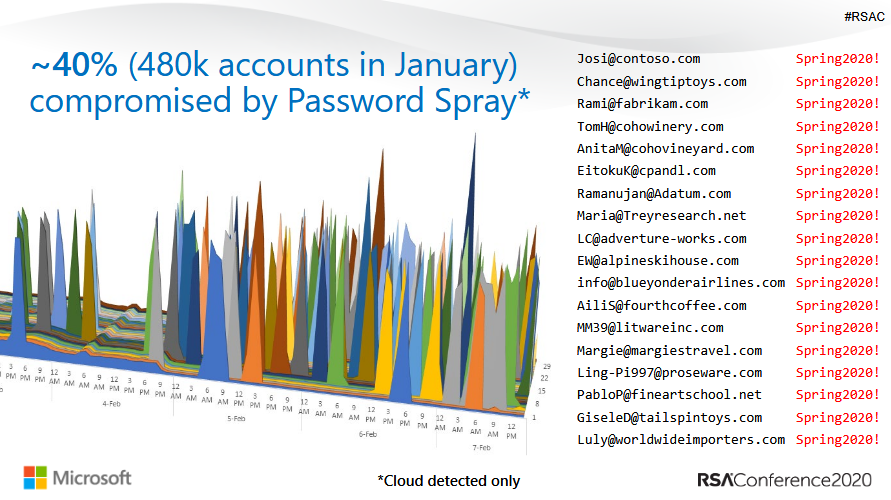
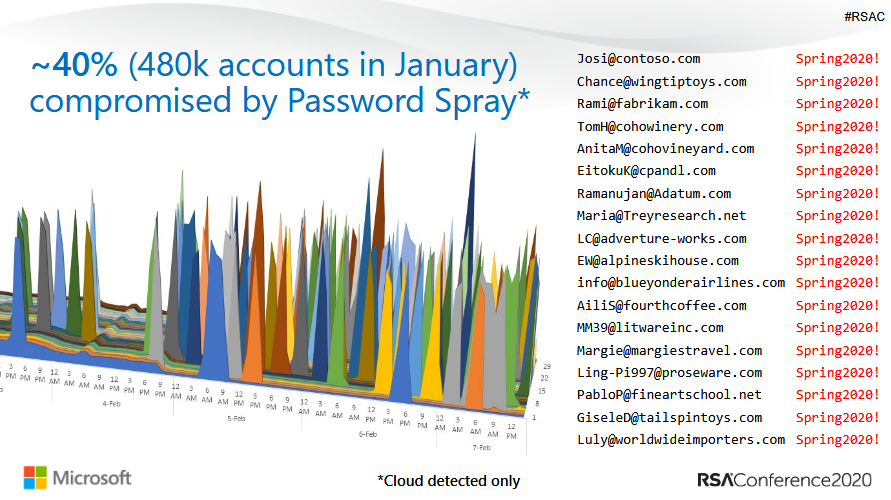
In most cases, the account hacks happen after rather simplistic attacks. The primary sources of most hacks of Microsoft accounts was password spraying, a technique during which an attacker picks a common and easy-to-guess password, and goes through a long list of usernames until they get a hit and can access an account using said password.
The second source of account hacks, Microsoft said, was password replays, a technique that involves an attacker taking credentials leaked at another company and then trying the same credentials on a Microsoft account, hoping the user reused usernames and passwords.
“We know that 60% of users reuse passwords. It’s super common,” said Lee Walker, Identity and Security Architect at Microsoft. “Don’t be confused. People reuse their enterprise accounts in non-enterprise environments.”
Walker said that the vast majority of password spraying and password replay attacks that take place on Microsoft’s infrastructure are carried out and target older legacy authentication protocols, such as SMTP, IMAP, POP, and others.
More precisely, 99% of all password spraying attacks and 97% of password replay attacks are carried out via legacy authentication protocols.
The reason, according to the cloud giant, is that these legacy authentication protocols don’t support MFA solutions, making them ideal for hackers.
Companies that leave these legacy authentication protocols enabled for their cloud systems and networks are exposed to attacks, and should disable them as soon as possible.
Per Microsoft, results are palpable, and they’ve seen a 67% reduction in account compromises for tenants who disable legacy authentication protocols
However, according to Microsoft, the first step for every company should be to enable an MFA solution for user accounts, first and foremost.
Microsoft has been telling companies and users alike to enable an MFA solution since last year, claiming that using an MFA solution — whatever that may be, hardware key, SMS, etc. — blocks 99.9% of all account hacks.
By Catalin Cimpanu for Zero Day | March 6, 2020 — 06:00 GMT (22:00 PST)